This guide is created specifically for a type of hack that adds keyword-heavy gibberish pages to your site, which we refer to as the cloaked keywords and links hack. It's written primarily for users of popular Content Management Systems (CMSs). However, if you don't use a CMS, you may still find this guide useful.
Identify the hack
The cloaked keywords and link hack automatically creates many pages with nonsensical text, links, and images. These pages sometimes contain basic template elements from the original site, so at first glance, the pages might look like normal parts of your site until you read the content.
The hacked pages are created to manipulate Google's ranking factors. Hackers often attempt to monetize this by selling the links on the hacked pages to different 3rd parties. Often the hacked pages also redirect visitors to an unrelated page where hackers can earn money.
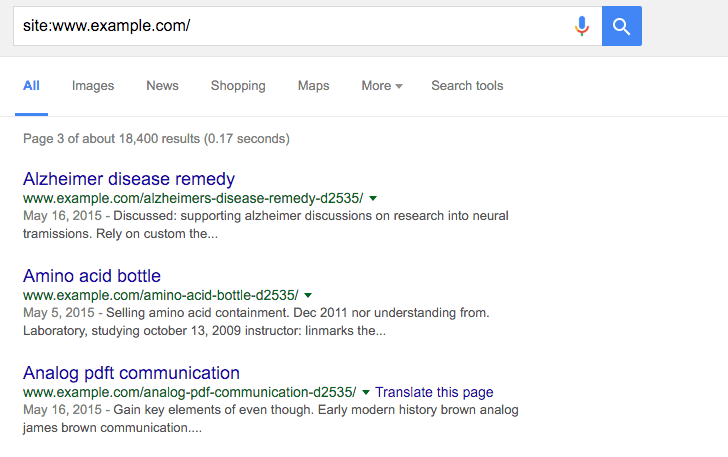
Start by checking the
Security Issues
tool in Search Console to see if Google has discovered any of these hacked pages
on your site. Sometimes, you can also uncover the pages by opening Google
Search and typing site:_your site url_, with the root level URL of
your site. The results of this search show the pages that Google has indexed for
your site, including the hacked pages. Look at a couple of pages of search
results to see if you spot any unusual URLs.
If you don't see any hacked content in Google Search, use the same search terms with a different search engine. Here's an example of what that may look like:
Typically, when you click a link to a hacked page, you're either redirected to another site or you see a page full of gibberish content. However, you might also see a message suggesting that the page doesn't exist (for example, a 404 error). Don't be fooled! Hackers try to trick you into thinking the page is gone or fixed when it's still hacked. They do this by cloaking content.
Check for cloaking by entering your site's URLs in the URL Inspection tool. The Fetch as Google tool lets you see the underlying hidden content.
Fix the hack
Before you start, backup your entire site offline. This ensures you can restore any files later, if necessary. Save all the files that are on your server to a location off your server.
If you use a content management system (CMS), such as WordPress or Drupal, you may be able to use a backup plugin to save your site. Remember to backup your database, too. Check your CMS's documentation to learn how.
Check your .htaccess file (3 steps)
The cloaked keywords and link hack uses your .htaccess file to automatically
create cloaked pages on your site. Familiarizing yourself with
.htaccess basics
on the official Apache site can help you understand better how the hack is
affecting your site, but it isn't required.
Step 1
Locate your .htaccess file on your site. If you're not sure where to find it
and you're using a CMS like WordPress, Joomla, or Drupal, search for
".htaccess file location" in a search engine along with the name of your CMS.
Depending on your site, you might see multiple .htaccess files.
Make a list of all of .htaccess file locations.
Step 2
Open the .htaccess file to view the contents in the file. Look for a line of
code that looks something like the following:
RewriteRule (.*cj2fa.*|^tobeornottobe$) /injected_file.php?q=$1 [L]
The variables on this line can change. Both cj2fa and tobeornottobe can
be any mix of letters or words. What's important is to identify the .php
that's referenced in this line.
Write down the .php file mentioned in the .htaccess file. In the example,
the .php file is named injected_file.php, but in reality the filename won't
be as obvious. It's usually a random set of innocuous words like
horsekeys.php or potatolake.php. This is likely to be a malicious .php
file that we need to track down and remove later.
Step 3
Replace all .htaccess files with a clean or default version of the .htaccess
file. You can usually find a default version of a .htaccess file by searching
for "default .htaccess file" and the name of your CMS. For sites with multiple
.htaccess files, find a clean version of each one and perform the replacement.
If no default .htaccess exists and you've never configured an .htaccess file
on your site, the .htaccess file you find on your site is probably malicious.
Save a copy of the .htaccess file(s) offline just in case and it
from your site.
Find and remove other malicious files (5 steps)
Identifying malicious files can be tricky and time-consuming. Take your time when checking your files. If you haven't yet, this is a good time to backup the files on your site. Look for the documentation from your particular CMS to learn how to backup your site.
Step 1
If you use a CMS, reinstall all the core (default) files that come in the default distribution of your CMS, as well as anything you may have added (such as themes, modules, plugins). This helps ensure that these files are clear of hacked content. You can search for "reinstall" and your CMS name to find re-installation instructions. If you have any plugins, modules, extensions, or themes, make sure to reinstall those as well.
Step 2
Start by looking for the .php file that you identified in the .htaccess
file earlier. Depending on how you're accessing the files on your server, you
should have some type of search function. Search for the malicious
filename. If you find it, first make a backup copy and store it in another
location just in case you need to restore it, then delete it from your site.
Step 3
Look for any remaining malicious or compromised files. You might have already removed all malicious files in the previous two steps, but it's important to confirm to ensure there aren't additional compromised files on your site.
You may feel overwhelmed if you think you have to open and look at every PHP file. Instead, create a list of suspicious PHP files that you want to investigate. Here are a few ways to determine which PHP files are suspicious:
- If you've already reloaded your CMS files, look only at files that aren't part of your default CMS files or folders. This should rule out a lot of PHP files and leave you with a handful of files to look at.
- Sort the files on your site by the date they were last modified. Look for files that were modified within a few months of the time that you first discovered your site was hacked.
- Sort the files on your site by size. Look for any unusually large files.
Step 4
Once you have a list of suspicious PHP files, check to see if they're malicious. If you're unfamiliar with PHP, this process might be more time-consuming, so consider brushing up on some PHP documentation. If you're completely new to coding, we recommend getting help. In the meantime, there are some basic patterns that you can look for to identify malicious files.
If you use a CMS, and aren't in the habit of editing those files directly, compare the files on your server to a list of the default files packaged with the CMS and any plugins and themes. Look for files that don't belong, as well as files that are larger than their default version.
First, scan through the suspicious files you've already identified to look for
large blocks of text with a combination of seemingly jumbled letters and
numbers. The large block of text is usually preceded by a combination of PHP
functions like base64_decode, rot13, eval, strrev, or gzinflate.
Here's an example of what that block of code might look like. Sometimes all this code is stuffed into one long line of text, making it look smaller than it actually is.
// Hackers try to confuse webmasters by encoding malicious code into
// blocks of text. Be wary of unfamiliar code blocks like this.
base64_decode(strrev("hMXZpRXaslmYhJXZuxWd2BSZ0l2cgknbhByZul2czVmckRWYgknYgM3ajFGd0FGIlJXd0Vn
ZgknbhBSbvJnZgUGdpNHIyV3b5BSZyV3YlNHIvRHI0V2Zy9mZgQ3Ju9GRg4SZ0l2cgIXdvlHI4lmZg4WYjBSdvlHIsU2c
hVmcnBydvJGblBiZvBCdpJGIhBCZuFGIl1Wa0BCa0l2dgQXdCBiLkJXYoBSZiBibhNGIlR2bjBycphGdgcmbpRXYjNXdmJ2b
lRGI5xWZ0Fmb1RncvZmbVBiLn5WauVGcwFGagM3J0FGa3BCZuFGdzJXZk5Wdg8GdgU3b5BicvZGI0xWdjlmZmlGZgQXagU2ah
1GIvRHIzlGa0BSZrlGbgUGZvNGIlRWaoByb0BSZrlGbgMnclt2YhhEIuUGZvNGIlxmYhRWYlJnb1BychByZulGZhJXZ1F3ch
1GIlR2bjBCZlRXYjNXdmJ2bgMXdvl2YpxWYtBiZvBSZjVWawBSYgMXagMXaoRFIskGS"));
Sometimes the code isn't jumbled and just looks like normal script. If you're not certain whether the code is bad, stop by our Google Search Central Help Community where a group of experienced webmasters can help you look over the files.
Step 5
Now that you know which files are suspicious, create a backup or a local copy by saving them on your computer, just in case any of the files aren't malicious, and delete the suspicious files from your site.
Check whether your site is clean
Once you're done getting rid of hacked files, check to see if your hard work paid off. Remember those gibberish pages you identified earlier? Use the Fetch as Google tool on them again to see if they still exist. If they respond as "Not Found" in Fetch as Google, chances are you're in pretty good shape and you can move on to fixing the vulnerabilities on your site.
How do I prevent getting hacked again?
The final step to prevent future hacks is to fix vulnerabilities on your site. A study found that 20% of hacked sites get hacked again within one day. Knowing exactly how your site was hacked is helpful. Read the top ways websites get hacked by spammers to start your investigation.
If you're unable to figure out how your site was hacked, follow this checklist to reduce vulnerabilities on your site:
- Regularly scan your computer: Use any popular virus scanner to check for viruses or vulnerabilities.
- Regularly change your passwords: Regularly changing the passwords to all your website accounts like your hosting provider, FTP, and CMS can prevent unauthorized access to your site. It's important to create a strong, unique password for each account.
- Use Two-Factor Authentication (2FA) or set up a Passkey: 2FA and passkeys make it significantly harder for hackers to sign in, even if they successfully steal your password.
- Update your CMS, plugins, extensions, and modules regularly: Many sites are hacked because they're running outdated software. Some CMSs support auto-updating.
- Consider subscribing to a security service to monitor your site: There's a lot of great services out there that can help you monitor your site for a small fee. Consider registering with them to keep your site safe.
Additional resources
If you're still having trouble fixing your site, we have a few more resources that might help you.
These tools scan your site and may be able to find problematic content. Other than VirusTotal, Google doesn't run or support them.
These scanners can't guarantee that they are able to identify every type of problematic content. Continue to check in on your site's security regularly.
Here are additional resources that can help you:
